Introduction: A Bold Move Against Online Extremism
In a sweeping crackdown on digital radicalization, the Justice Department seizes several websites it says spread terrorist propaganda — sending a clear message to extremist networks operating in the shadows of the internet. This action marks one of the most significant federal efforts to dismantle the online infrastructure that fuels real-world violence.
But what exactly does this mean for everyday internet users, civil liberties advocates, and national security professionals? And how does the U.S. government legally justify taking down websites in the first place?
This article dives deep into the details of the seizures, the legal framework that enables them, what types of content triggered federal action, and what you should know as a citizen navigating an increasingly monitored digital world.
What Happened? A Breakdown of the Justice Department’s Website Seizures
The U.S. Department of Justice, working alongside the FBI and other federal partners, moved to seize control of multiple websites alleged to have hosted, distributed, or amplified terrorist propaganda. These platforms were not fringe corners of the dark web alone — several operated on the open internet, accessible to anyone with a search engine.
Which Websites Were Targeted?
While specific domain names vary across operations, the DOJ has historically targeted websites associated with:
- ISIS (Islamic State) recruitment and propaganda arms
- Al-Qaeda-affiliated media networks
- Domestic extremist groups promoting violence against government institutions
- Pro-Hamas digital channels distributing inflammatory content
In the most recent wave of seizures, federal investigators identified websites that were actively used to:
- Recruit new members into designated terrorist organizations
- Distribute videos, manifestos, and instructional materials
- Solicit cryptocurrency donations to fund violent activities
- Coordinate messaging across multiple social platforms
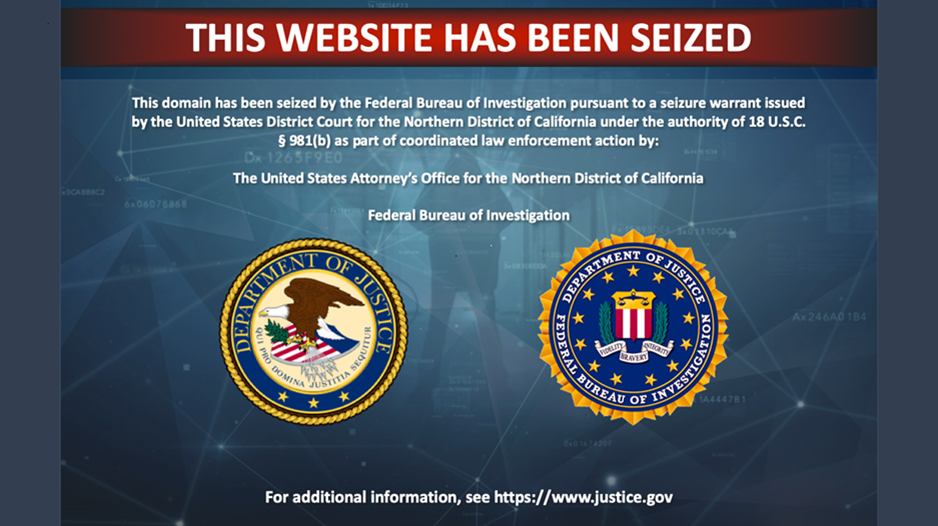
The seized domain names now display a digital seizure banner — a stark notice from the DOJ informing visitors that the site has been taken over by U.S. federal authorities.
The Legal Authority Behind the Seizures
One of the most common questions people ask is: Can the government just take down a website? The answer is yes — under very specific legal conditions.
How the DOJ Justifies Domain Seizures
The Justice Department relies on several legal tools to seize websites:
- 18 U.S.C. § 981 — Civil asset forfeiture laws that allow the government to seize property used in connection with federal crimes
- The Providing Material Support to Terrorists Statute (18 U.S.C. § 2339A/B) — Makes it illegal to provide resources, including digital infrastructure, to designated terrorist organizations
- Court-issued seizure warrants — Federal judges must approve the action before any domain is taken offline
This is not a unilateral decision. A federal judge reviews the evidence and authorizes the seizure. The DOJ must demonstrate probable cause that the website was being used as an instrument of terrorism or material support for a designated foreign terrorist organization.
The Role of OFAC and Designated Terrorist Organizations
The Office of Foreign Assets Control (OFAC) maintains a list of Specially Designated Nationals (SDNs) — including terrorist groups. When a website is found to be connected to an SDN-listed entity, operating or funding that site becomes a federal violation, enabling the DOJ to pursue asset forfeiture, which includes digital assets like domain names.
Why This Matters: The Real-World Impact of Online Terrorist Propaganda
The phrase “it’s just a website” dramatically undersells the damage these platforms cause. Research consistently shows that online radicalization is a genuine and growing threat.
How Online Propaganda Fuels Real Violence
Consider the following:
- The 2019 Christchurch mosque shootings in New Zealand were livestreamed and the shooter’s manifesto spread virally across extremist websites within minutes
- The 2021 U.S. Capitol attack was coordinated largely through online platforms, including fringe websites and forums
- Multiple lone-wolf terrorist attacks in Europe and the U.S. have been traced back to individuals radicalized through online propaganda channels
These are not hypothetical scenarios. The websites targeted by the Justice Department are not passive observers — they are active tools in the radicalization pipeline, moving vulnerable individuals from curiosity to commitment to violence.
Who Is Most at Risk?
Radicalization online tends to target:
- Young men aged 16–30 experiencing social isolation or identity crises
- Individuals with grievances — real or perceived — against governments, ethnic groups, or religious institutions
- People in online echo chambers already exposed to extreme ideological content
Removing these websites disrupts the radicalization funnel at its source.
Free Speech vs. National Security: The Ongoing Debate
Not everyone applauds these seizures. Civil liberties organizations and First Amendment advocates raise legitimate questions about government overreach.
Where the Line Gets Drawn
The First Amendment protects a remarkable amount of speech — even hateful, offensive, or politically extreme speech. However, courts have consistently held that certain categories of expression fall outside First Amendment protection, including:
- Incitement to imminent lawless action (Brandenburg v. Ohio, 1969)
- True threats — statements conveying a serious intent to commit violence
- Material support for terrorism — even when that support takes the form of speech or media
The DOJ’s seizures, when legally executed, fall into these unprotected categories. The websites targeted were not merely expressing unpopular opinions — they were actively facilitating recruitment, funding, and operational coordination for organizations the U.S. government has formally designated as terrorist.
What Critics Still Get Right
That said, some watchdog groups point to the risk of mission creep. Key concerns include:
- Vague definitions of what constitutes “propaganda” versus political speech
- Chilling effects on journalists and researchers who study extremist content
- Lack of transparency in how targets are selected and warrants are obtained
These concerns deserve serious attention. Oversight mechanisms — including congressional review and judicial scrutiny — are essential safeguards against abuse.
What Tech Companies and Website Owners Should Know
If you operate a website, host a platform, or work in digital communications, the DOJ’s actions carry important practical implications.
Practical Tips for Website Owners and Platforms
- Review your Terms of Service — Ensure your platform explicitly prohibits content that supports or glorifies terrorist organizations
- Implement content moderation — Automated tools and human review can catch extremist content before it becomes a federal liability
- Know your hosting provider’s policies — Many major hosting services cooperate with federal law enforcement and will comply with valid legal orders
- Train your team — Employees should know how to identify and escalate extremist content to legal counsel or law enforcement
- Respond promptly to legal notices — If your platform receives a DOJ inquiry or preservation request, consult legal counsel immediately
What to Do If You Encounter Terrorist Propaganda Online
If you come across a website or social media account promoting terrorist propaganda:
- Do not share or amplify the content
- Report it to the platform directly using their abuse or safety reporting tools
- File a tip with the FBI at tips.fbi.gov — the agency has a dedicated portal for online terrorist content
- Contact NCMEC or DHS if the content involves minors being recruited
How the DOJ’s Actions Fit Into the Broader Global Strategy
The United States does not act alone in this space. Website seizures are part of a coordinated international effort to dismantle the digital infrastructure of global terrorism.
Key International Partnerships
- Europol’s Internet Referral Unit (IRU) works with tech companies to flag and remove terrorist content across the EU
- The Global Internet Forum to Counter Terrorism (GIFCT) is a coalition of major tech companies — including Meta, Google, and Microsoft — that share hash databases of known terrorist content
- Five Eyes intelligence alliance — comprising the U.S., UK, Canada, Australia, and New Zealand — coordinates intelligence sharing on digital terrorism threats
Together, these partnerships create a layered response that makes it significantly harder for terrorist organizations to maintain a stable online presence.
What Comes Next: Trends in Digital Counter-Terrorism
The seizure of terrorist propaganda websites is not a one-time event — it is part of an accelerating trend.
Emerging Developments to Watch
- AI-generated propaganda — Terrorist organizations are beginning to use generative AI to produce high-quality recruitment content at scale; the DOJ and its partners are developing detection tools to counter this
- Decentralized platforms — Extremists are migrating to blockchain-based and peer-to-peer platforms that are harder to seize; law enforcement is adapting its legal toolkit accordingly
- Cryptocurrency tracing — Many seized websites solicited Bitcoin and Monero donations; the DOJ’s new crypto tracing capabilities are making it easier to follow the money and identify organizers
- Expanded asset forfeiture — Expect future actions to target not just domain names but hosting accounts, email servers, and associated financial accounts
Conclusion: A Necessary Fight With Important Safeguards
The fact that the Justice Department seizes several websites it says spread terrorist propaganda is not just a headline — it is a window into one of the defining security challenges of the digital age.
These actions disrupt real recruitment pipelines, cut off funding channels, and deny violent extremists the megaphones they need to spread their message. At the same time, the government’s power to remove online content must always be exercised with transparency, judicial oversight, and respect for constitutionally protected speech.
The battle against online radicalization will not be won with a single press release or a batch of seized domain names. It requires sustained collaboration between law enforcement, the technology industry, civil society, and an informed public.
Stay informed. Report suspicious content. And demand accountability from those who wield the power to shape what exists — and what disappears — on the internet.